Auto-add Git committers to your team
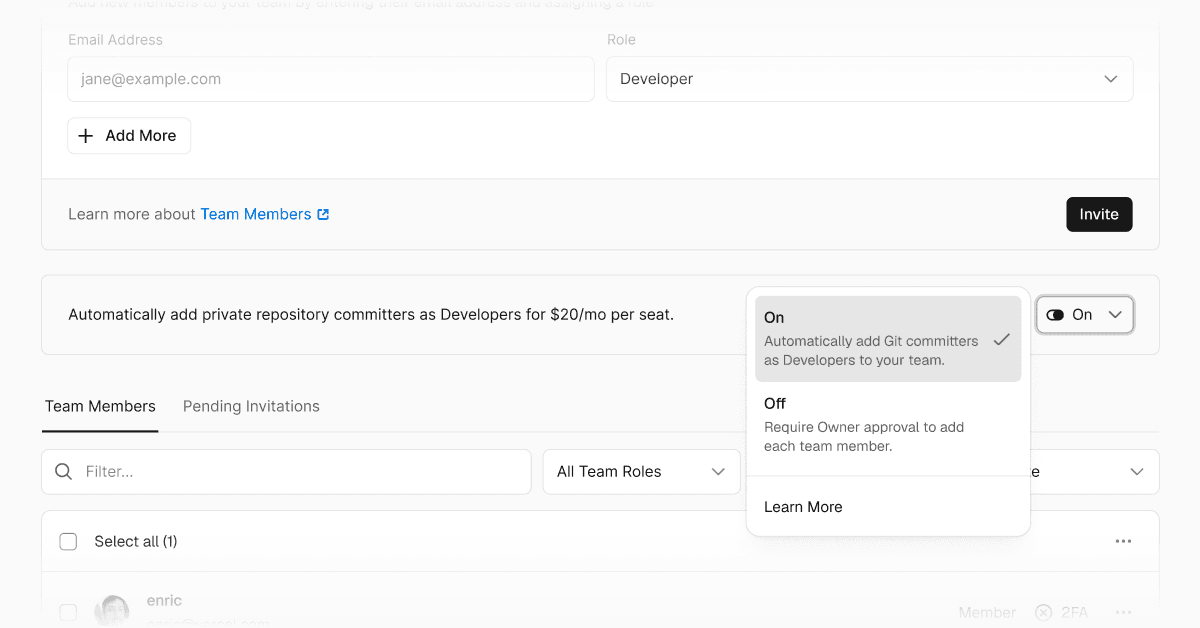
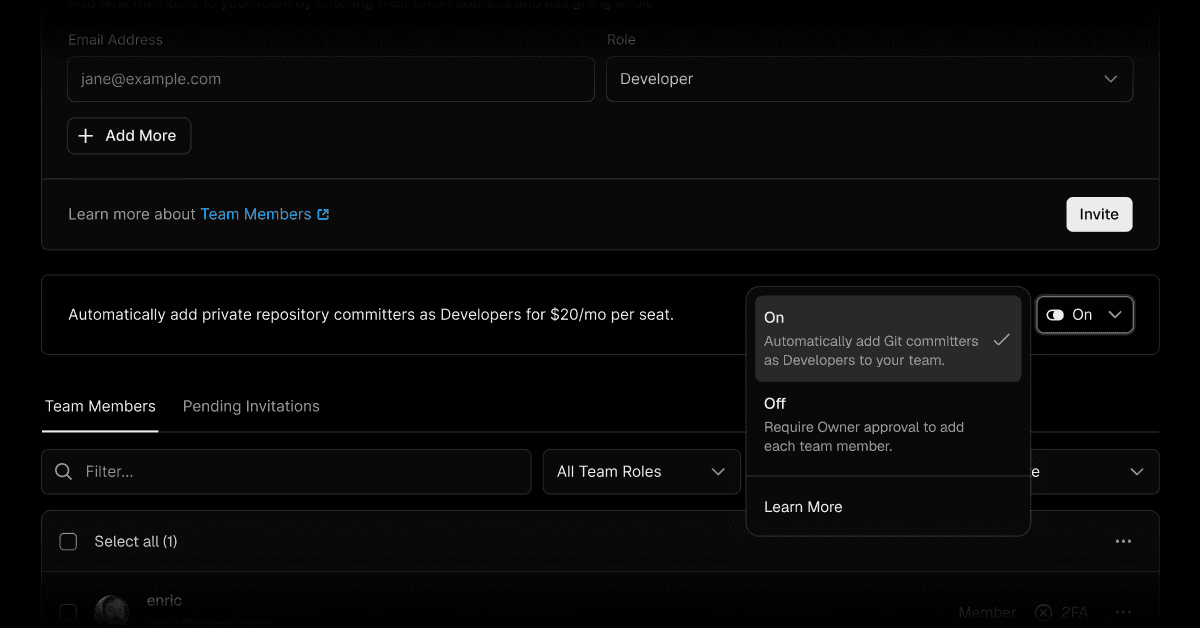
Pro teams can now choose how Git committers to private repositories are added to their Vercel team.
Auto Approval: non-team committers with Vercel accounts are automatically added to your team and their deployments proceed immediately. Added members count toward your team seats at standard Pro pricing.
Manual Approval: deployments are blocked until an owner approves the new member.
Choose your approval preference in team settings.
Learn more about collaboration settings and troubleshooting project collaboration.